K–12 doesn’t need sci-fi identity wallets to benefit from self-sovereign data. See how districts can use ecosystem orchestration and tokenization to regain control of student data today.
From “Just Make It Work” to “Who Actually Controls This Data?”
Ten years ago, most districts were just trying to get students into apps without losing instruction time. SSO, automated rostering, and identity platforms felt like the finish line: accounts created, classes synced, teachers happy.
Today, those same tools sit on top of an app ecosystem where every new product wants its own copy of student and staff data. Names, IDs, enrollments, accommodations, assessment histories, copied again and again into vendor databases you don’t control. It worked when you had a handful of systems. It doesn’t work when you have hundreds of systems, AI everywhere, and parents asking very specific questions about where their child’s data lives.
That’s the gap self-sovereign concepts are trying to close, not as a futuristic credential wallet, but as a very practical shift in who controls student data, how it moves, and when access actually ends.
The Core Problem: Data Sprawl, Not Just Weak Security
Most districts don’t suffer from a lack of security tools. The real problem is structural: a copy-and-sync integration model that breaks containment by design. Other K–12 security partners have traced similar challenges as districts mature their student data security programs.
Here’s what that looks like in practice:
- A small number of “source of truth” systems (SIS, HR, LMS) feed dozens or hundreds of external tools.
- Each tool gets its own slice of PII in its own schema, stored on its own infrastructure.
- When enrollments change or access should be revoked, you depend on a tangle of syncs, CSVs, and vendor processes to keep up.
Between July 2023 and December 2024 alone, more than 14,000 security events and 9,300 confirmed cyber incidents were recorded across over 5,000 U.S. K–12 organizations. That’s not just bad luck. It’s what happens when the easiest way to integrate is to copy data out of your control.
Self-sovereign concepts don’t fix this by adding yet another dashboard. They fix it by changing the default: stop making new copies of student and staff data every time you approve an app.
What Self-Sovereign Ideas Look Like in K-12
When people hear “self-sovereign,” they often jump straight to blockchain or student-held credentials. That’s one possible destination, but it’s not where K–12 needs to start.
In a district context, “self-sovereign” can be translated into three practical principles:
- Data authority stays with the district.
The district remains the source of truth. Vendors get governed access, not custody, of student data. For international or cloud‑hosted environments, this also intersects with data sovereignty, where student data is physically stored and which country’s laws apply to it. - Data is exchanged, not handed over.
Instead of pushing full records into each vendor system, you issue purpose-limited claims: “This user is a Grade 4 student at School B,” not “Here is their full SIS record.” - Access is observable and revocable by design.
When a contract ends, a program closes, or a risk appears, you can turn off access centrally without hunting through every vendor’s database.
You don’t need to change your entire identity stack to start. You need a different control plane for how data moves between you and your vendors.
Tokenization: The Bridge Between Today’s Reality and Self-Sovereign Control
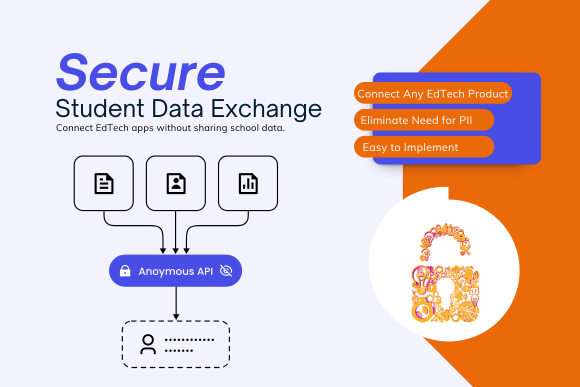
This is where SchoolDay’s view is opinionated: tokenization is the practical bridge between today’s integrations and tomorrow’s self-sovereign posture.
Instead of sending raw identifiers everywhere, the district issues tokens and derived attributes that are meaningful only within a controlled context:
- Rostering exchanges use pseudonymous IDs instead of SIS IDs.
- Analytics tools receive attributes (grade band, program membership) rather than full demographics.
- Apps authenticate through SSO but never store complete identity profiles locally.
Underneath, SchoolDay’s zero-trust ecosystem orchestration acts as a staging layer. Data remains anchored to district systems; the vault governs what can be shared, with whom, for what purpose, and for how long. Vendors see only what they need, and districts can trace exactly which app touched which data, when.
This is self-sovereign thinking applied to K–12’s actual constraints: you keep your existing SIS, LMS, and identity stack, but you stop treating “copy the data” as the only integration pattern.
Orchestration: Governing the Space Between Schools and Vendors
The most serious failures don’t happen inside one system. They happen in the space between systems, where permissions get over-scoped, data is reused in ways no one anticipated, and deletion never quite catches up.
Ecosystem orchestration gives you a way to govern that space:
- A neutral control layer sits between the district and every vendor.
- Application approval, data minimization, and risk review plug into the same backbone.
- Policies, not ad hoc integrations, decide what data each app can see.
Within SchoolDay, that orchestration is backed by zero-trust assumptions: no vendor is implicitly trusted with “everything,” and no app receives more data than its documented purpose justifies. When an AI-powered tool enters the picture, you can constrain its inputs at the edge instead of hoping its terms of service do the right thing with your students’ PII.
For school leaders, this changes the conversation with your teams:
- From “Can we connect this app by next week?”
- To “What is the minimum data this app truly needs, and how do we enforce that automatically?”
What This Means for Your Next Procurement Cycle
You don’t have to put “self-sovereign” in your RFPs to benefit from these concepts. You can start with three concrete expectations for every new tool:
- No unnecessary copies of core records.
Ask vendors how they can operate with tokenized or minimized data rather than full SIS extracts. If their answer depends entirely on nightly CSVs, treat that as a risk signal. - District-anchored governance.
Insist on an architecture where your district remains the authority for identity and eligibility, and where access can be revoked centrally—not just through ticketing a vendor. - Continuous visibility into what’s being used.
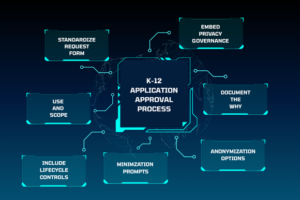
Require the ability to see, in one place, which apps have access to which data categories, and adjust those scopes over time without rebuilding integrations. Districts that modernize their vendor application approval process can treat this as a default expectation,not a future wish list.
SchoolDay is not another point solution. It is the infrastructure that lets you implement self-sovereign data principles with the systems you already own. You get the benefits of tighter control, reduced vendor risk, and cleaner AI adoption, without asking your teams to become identity theorists.