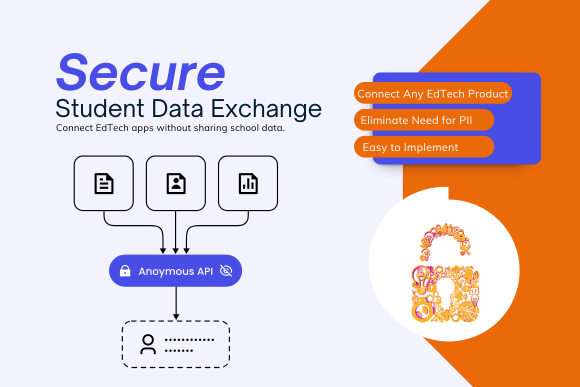
K-12 districts struggle to balance teacher requests for new edtech tools with student data privacy requirements. Schools are obligated to keep student data safe, yet the moment a new app is connected is often when risk quietly spikes. A disciplined application approval process can instead become the front line of selective disclosure and data minimization, especially when districts pair it with tokenized, zero‑PII integrations.
This article helps K–12 leaders redesign their application approval process so every new request becomes a privacy checkpoint, not just a purchasing step, establishing application requests as the place where districts practice self‑sovereign‑style selective disclosure by proving just enough about students for tools to work, without oversharing personally identifiable information (PII).
What Is a District Application Approval Process?
A district application approval process is a standardized workflow that evaluates new educational technology tools for instructional value, data privacy compliance, and security risk before granting access to student information. An effective approval process includes a formal request form, data minimization checkpoints, governance review, and minimal-data integration patterns.
Quick takeaway: Districts can reduce student data risk by treating every application request as a selective disclosure decision, sharing only the minimum claims (grade level, enrollment status) rather than full student records, and using tokenized identifiers instead of persistent IDs wherever possible.
Why Informal Application Approval Requests Create Hidden Student Data Risk
Without a formal application approval process in place, district leaders struggle to keep track of who has access to student data or how to end that access when an app is no longer being used. A teacher might discover an app and send an email to IT or mention it in the hallway, with no formal request form or standardized process.
Without considering privacy and data scope up front, requests may be evaluated mainly on instructional value or content. And unfortunately, there is often an automatic assumption that if an application is approved, it gets full roster and account data “because that’s how integrations work.”
The consequences:
- Unvetted or under-vetted apps holding large volumes of PII and sensitive data.
- Difficulty complying with FERPA, state privacy laws, and data governance checklists because no one sees the full picture of vendor access.
- Shadow IT: apps already in use before anyone in IT, legal, or compliance has reviewed data sharing agreements.
To reduce risk meaningfully, the application approval process needs to become the place where the district refuses to overshare by default and where technical teams have options to send only minimal, tokenized data rather than full student information system records.
Treat Every Application Approval Request as a Selective Disclosure Decision
Self‑sovereign data models emphasize user control and selective disclosure: sharing proofs like “in grade 7” or “over 13” instead of full identity records. For school districts, the application approval process is where you decide which claims a tool actually needs versus which raw fields you’ve simply been used to providing.
That shift to a more secure student data exchange starts with reframing one core question:
Old question: “What does this app want from the SIS or rostering feed?”
New question: “What is the least revealing information we can provide so this app still works?”
Examples of selective disclosure in practice:
- Instead of providing a specific date of birth, share “over 13” or a grade band if that is sufficient for COPPA compliance and functionality.
- Instead of full home address and parent contact information for every app, restrict those fields to tools that directly need them for communication or safety purposes.
- Instead of state IDs or persistent district identifiers, provide pseudonymous tokens that are meaningful only within that app’s context.
In an orchestrated, token-based ecosystem, this approach goes further: the app doesn’t see raw fields at all, only a token or attribute that encapsulates the claim it needs (for example, a group membership or eligibility flag), while the district retains the underlying identity data in its own systems.
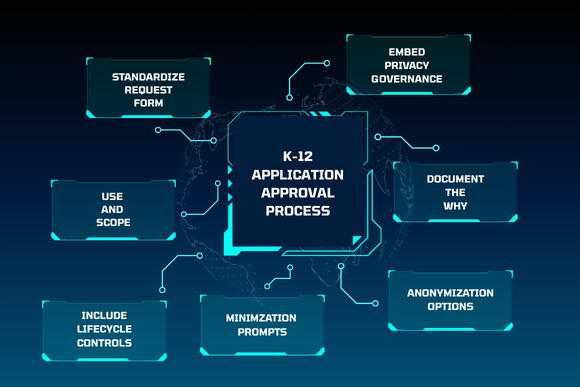
5 Steps to Build Data Minimization into your Application Approval Process Form
The easiest way to make minimization non‑negotiable is to hard‑wire it into the request workflow itself.
1. Standardize the Form
Require all application approval requests to use one digital form for all requests—no email, chat, or verbal approvals. Make the form easy to find on your intranet or staff portal.
2. Capture Use and Scope
Form sections should cover:
- Intended instructional or operational use.
- Student and staff groups in scope (grade levels, schools, specific classes).
- Data categories requested, using checkboxes rather than free text (names, birthdates, addresses, grades, assessment scores, etc.).
3. Add Minimization Prompts
For each data category checkbox, include follow-up prompts such as:
- “Why is this specific field necessary for the app to function?”
- “Could a less-detailed attribute (for example, grade band instead of DOB) work instead?”
- “What happens in this app if we withhold this field?”
These prompts shift responsibility: requesters must justify data needs instead of IT or governance teams guessing intent.
4. Offer Anonymization Options
Ask explicitly: “Can this app operate with pseudonymous tokens or local IDs instead of state IDs or district-wide student identifiers?”
Many apps can function with anonymized identifiers that are meaningful only within that specific tool, significantly reducing exposure if the vendor is breached.
5. Document the “Why” for Every Field
The form should ensure that every requested data element has a documented justification that ties back to a specific function or compliance requirement. This documentation becomes essential during audits, vendor renewals, and when reducing data scopes over time.
Using this framework, the form itself becomes a mechanism for selective disclosure, ensuring requesters participate in minimization rather than IT carrying that burden alone.
Use Tokenization and Pseudonymous IDs Wherever Possible
In many cases, educational apps can operate with pseudonymous tokens or local IDs instead of state IDs or other persistent identifiers. Rather than receiving detailed information about each student, the app receives an anonymized identifier or token that represents the student only within that app’s context and only the specific attributes strictly needed (for example, class membership, grade level, or eligibility status like “receives Title I services”).
In a zero-trust ecosystem‑orchestration model, the platform maps those tokens back to real students internally, so data returning from the app, such as grades, progress, or assessment results, can be de‑anonymized and reconciled without ever exposing full student records to the vendor.
This approach aligns closely with self‑sovereign principles: the district maintains control of identities and shares only minimal, revocable claims externally.
Make Privacy Governance Visible in the Application Approval Workflow
The application approval process should not be an isolated function. It needs to be embedded inside your school’s broader data governance structure. Submissions should be routed to a cross-functional governance team that includes:
- IT (security, infrastructure, integration)
- Curriculum and instruction (instructional value)
- Legal or compliance (contracts, DPAs, FERPA alignment)
- School leadership (budget, priorities)
Use RACI to Clarify Roles
Define who Recommends (IT, curriculum), who is Accountable for final approval (often CTO or data officer), who must be Consulted (legal, finance), and who is Informed (principals, teachers).
Include Mandatory Checkpoints
Every application approval request should pass through these reviews before approval:
- Policy alignment: Does the app’s purpose and data flow align with existing privacy, security, and acceptable use policies?
- Data protection expectations: Do minimization, storage limitation, security controls, and vendor transparency align with your standards and contract requirements?
- Data location and sovereignty: Where will data be stored, and does that comply with state, federal, or local legal requirements?
Provide clear, timely feedback.
Requesters should receive responses in a reasonable timeframe (suggest 5–10 business days for standard requests):
- Approved – app can proceed with specified data scope.
- Approved with reduced scope – app is approved but with fewer data fields than requested.
- Deferred – needs more information or contract negotiation.
- Declined – does not meet privacy, security, or instructional standards.
All decisions should include brief reasons tied explicitly to data and privacy outcomes, not vague denials.
Designing a Minimal Data Integration Pattern for Approved Apps
Approval should never automatically mean “give the app everything the feed can provide.” Baseline integration should always be minimal data, explicitly documented and enforced through your orchestration or integration layer.
Best practices for minimal data integrations:
- Use curated data views or tokenized outputs rather than raw database tables wherever possible.
- During pilot phases with new apps, consider zero‑PII trials: no live student data until functionality and instructional value are validated using test accounts or anonymized data.
- Prefer apps and integration patterns that support anonymization and tokenization while still delivering required functionality.
- Document explicitly which fields are being shared and why, so future reviews can tighten scopes as needs change.
Documentation for Every Approved App
For every approved application request, maintain a simple, searchable record that includes:
- Purpose: What instructional or operational need does this app meet?
- Data elements or claims shared: Specific fields (or token types) the app receives.
- Legal basis and contract reference: Link to signed DPA, terms of service, or BAA.
- Storage location and retention expectations: Where data lives, how long it’s kept, and how deletion is verified.
Over time, this record becomes a living map of where student data actually flows, making it easier to adjust scopes, respond to audits, or revoke access centrally.
Build Lifecycle Controls in From the Start
Managing student data privacy in K–12 is not just about how data starts flowing; it is also about when and how data access stops.
Time-Bound Approvals
Set explicit review dates for all apps, especially pilots. A standard pattern:
- Pilots: Review after one term or semester
- Established tools: Annual review of continued need, usage, and data scope
After each review period, the app must be explicitly re-approved rather than continuing indefinitely by default.
Exit Strategies Should Be Baked into the Application Approval Process
The application request form should require requesters and governance reviewers to answer:
- “What happens to the data when our contract or pilot ends?”
- “How will deletion or anonymization be verified?”
- “Who is responsible for confirming data disposition?”
Clear Offboarding Process
When an app is retired, your process should include:
- Revoke user access via SSO.
- Terminate data feeds and integrations.
- Verify that vendor deletes or returns data per contract.
- Remove the app from approved lists and catalogs.
- Update internal documentation.
When the application approval process and app integration are managed through an orchestration layer, revoking access and stopping feeds can be operationalized as policy changes rather than one‑off technical tasks, further reducing the chance of forgotten data exposures or “zombie” integrations.
Making the Process Usable for Teachers and Staff
A strong application approval process protects students, but it also needs to avoid creating so much friction that teachers work around it.
Reduce Friction without Weakening Controls
- Keep the first part of the form simple: basic use case, target audience, and general data needs.
- Push detailed privacy and technical questions to the governance review stage where possible.
- Offer a public, easy-to-search approved app catalog so teachers can see what’s already vetted and ready to use, reducing duplicate requests.
Provide Communication and Training
- Use brief, scenario-based training to show how this process protects students and staff, linking to real examples of edtech privacy failures or “scary app” lists.
- Provide simple guidance on red flags in vendor privacy policies, such as:
- Broad data reuse for marketing or product development
- Unclear or indefinite retention
- Sharing with third-party advertisers or analytics platforms
Shifting the Culture
Emphasize that the goal is not to say “no” more often, but to say “yes, safely” by sharing less data and retaining more district control over vendor relationships.
Frequently Asked Questions About District App Request Processes
Q: What data should schools share with educational apps?
Schools should share only the minimum data necessary for the app to function, preferably anonymized tokens and attributes (like “Grade 7” or “over 13”) rather than full student records including names, birthdates, and home addresses. Following FERPA guidelines and state student privacy laws, districts should default to selective disclosure and data minimization.
Q: How can districts reduce risk when approving new edtech apps?
Use a formal application approval process with a cross-functional data governance review, require vendors to justify every requested data field, implement zero-PII trials during pilot phases, and design integrations that use tokenized identifiers instead of raw PII. Pair this with time-bound approvals and clear exit strategies.
Q: What is selective disclosure in K-12 data privacy?
Selective disclosure empowers students, families, and educators to share only the specific information required for a learning activity, service, or system while keeping all other personal data private and under their control. In a K–12 environment, this approach supports self-sovereign data practices, ensuring schools can verify what they need without over-collecting or exposing sensitive student information.
Selective disclosure means sharing specific claims or proofs about a student (such as enrollment status, grade band, or age verification like “over 13”) rather than exposing full identity records. This approach reduces privacy risk if a vendor is breached and aligns with self-sovereign data principles.
Q: How long should app approvals last?
Application approvals should be time-bound with explicit review dates, typically one year for established apps and one term or semester for pilots, to ensure data access remains necessary, appropriate, and aligned with current instructional needs and vendor security postures.
Q: What happens if a teacher uses an app without going through the application approval process?
This is often called “shadow IT” and creates significant risk. Districts should communicate clearly that unapproved apps may violate FERPA, state privacy laws, and district policy. Provide an easy application approval process and approved app catalog to reduce the temptation to bypass governance and conduct periodic scans to identify unauthorized tools.
A Practical Path Toward Self-Sovereign Data Management
By adhering to this framework, the application approval process becomes the first moment you plan for minimization and eventual revocation, not an afterthought. Over time, districts following this approach should see:
- Fewer copies of full student records across third-party systems
- More use of limited claims and tokenized identifiers instead of raw PII
- Clearer, more centralized control over every vendor data relationship
- Faster response to audits, parent requests, and regulatory inquiries
This is what a self-sovereign-style posture looks like in practice for K–12: the district retains authority over student data, shares only what is necessary through governed, tokenized exchanges, and can change or revoke those disclosures without losing visibility or control.
The most effective way to reduce student data risk is to treat the application approval process as a privacy control, not just a procurement step. By embedding data minimization prompts into request forms, using tokenized integrations, and building lifecycle controls from the start, K-12 districts can achieve the kind of data authority that self-sovereign principles promise—fewer unnecessary data exposures, stronger governance, and clear control over every vendor relationship in the edtech ecosystem.