This article presents a practical K–12 data minimization and access control playbook that shows how districts can share less student data, reduce risk, and adopt self-sovereign-style selective disclosure across their ecosystems.
“Do we actually need to share all of this data?” is one of the most powerful questions a district can ask. Data minimization is more than a legal phrase in FERPA guidance; it is a practical strategy for reducing risk while keeping classrooms running smoothly.
In K–12, data minimization and access control are the everyday expressions of a self-sovereign mindset: the district decides what to share, when, for how long, and with whom, often by disclosing only proofs or attributes rather than full records. This playbook is designed to help you put that idea into practice.
Step 1: Start With Purpose, Not Fields
Most over-collection happens because districts begin with a roster template instead of a purpose statement. Flip that sequence.
- For each application, define the instructional or operational purpose in plain language.
- List which decisions or experiences depend on student data (e.g., placement, access control, personalization).
- Map backwards from that purpose to the minimum attributes required: grade level, course enrollment, eligibility flags, or age band, rather than full demographics.
When you lead with purpose, full names, dates of birth, and addresses often fall away as unnecessary for many tools.
Step 2: Practice Selective Disclosure
Self-sovereign-style selective disclosure means sharing proofs, not full identities. In K–12, that can be surprisingly concrete.
- Replace “date of birth” with “over 13” for COPPA-related tools.
- Replace “full grade history” with “enrolled in Algebra I this term.”
- Replace “full student ID” with a context-specific token that only has meaning within one app or integration.
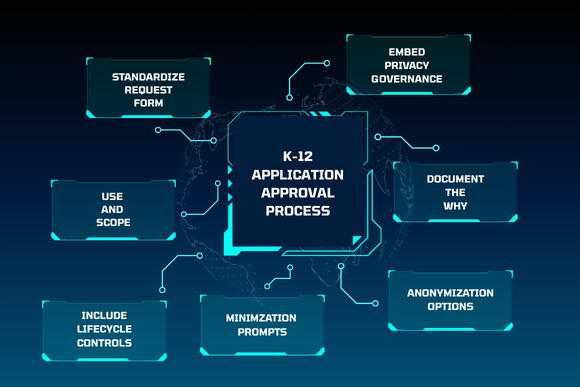
Your application approval process is the natural place to enforce this. Each new request should answer: “Which specific claims does this app truly need, and can we provide them as limited attributes or tokens instead of raw PII?”
Step 3: Minimize Copies, Not Just Fields
Even a perfectly minimized roster can become risky if it is copied and stored in dozens of places. Data minimization also means reducing how many systems hold sensitive information at rest.
- Favor integrations where apps reference centralized, district-controlled data instead of storing their own full database.
- Use tokenization to replace persistent identifiers with non-reversible tokens, so downstream systems never see raw student IDs or contact details.
- Design data retention rules so vendor systems automatically purge data that is no longer needed for their purpose.
Over time, this “share less and store less” posture shrinks your breach surface and simplifies audits and right-of-access requests.
Step 4: Align Access Control with Minimization
Data minimization is incomplete without matching access control. If everyone can see everything, you are still over-exposed.
- Implement role-based access: define which roles in your district can see which data classes (e.g., counselors vs. classroom teachers vs. vendor support).
- Tie access to clear purposes and time windows; for example, granting a vendor temporary access to de-tokenized records only for a specific migration or support task.
- Log and audit: maintain a record of who accessed what, when, and why, so you can demonstrate that selective disclosure is being honored in practice.
In a self-sovereign-style model, access is not permanent; it is granted, time-limited, monitored, and revocable.
Step 5: Build Self-Sovereign Patterns into Everyday Workflows
The most sustainable way to practice data minimization is to bake it into the workflows staff already use, instead of adding extra hoops.
- Embed minimization prompts in app request forms: require requesters to explain what data the tool truly needs and why.
- Use zero-trust ecosystem orchestration or vault services to handle token generation, selective disclosure, and just‑in‑time de‑tokenization, so staff do not manage cryptography themselves.
- Provide simple guidance for educators: for example, “Always prefer approved, tokenized tools over entering student names into public AI systems.”
When minimization, tokenization, and access control are handled by the underlying ecosystem, not just by policy documents, districts move closer to a genuine self-sovereign posture: sharing less, knowing more, and retaining authority over every disclosure.
Every minimized field and every avoided copy is a concrete privacy win for your students. Use this playbook as a starting point to revisit your app approval process, tighten scopes with your highest-risk vendors, and pilot self-sovereign-style selective disclosure in one or two key integrations. When your district is ready to embed minimization and tokenization into the architecture itself, SchoolDay can help you design a data environment where “sharing less and protecting more” becomes the default.
Key Takeaways
- Effective data minimization starts with purpose: districts should define what an app is trying to achieve, then work backward to the minimum data attributes needed.
- Self-sovereign-style selective disclosure means sharing proofs and limited attributes—such as “over 13” or “enrolled in Algebra I”—instead of full identity records.
- Minimizing data is not only about shrinking field sets; it also requires reducing the number of systems that store copies of sensitive information.
- Aligning minimization with role-based access, auditing, and tokenization helps districts turn “share less and protect more” into a default operating model rather than a one-time project.